
|
RootKit Hook Analyzer Check for active kernel rootkits on your system version 3.00 allows you to test system hook quality |
Please note: support and development of this product have been discontinued. Functionality
of this product can be found in SanityCheck.
RootKit Hook Analyzer is a security tool which will check if there are any rootkits
installed on your computer which hook the kernel system services. Kernel RootKit Hooks are
installed modules which intercept the principal system services that all programs and the
operating system rely on. If any of these system services are intercepted and modified
it means that there is a possibility that the safety of your system is at risk and that
spyware, viruses or malware are active.
Are kernel hooks always bad ?
Kernel hooks are out of fashion these days and not officially documented and considered
deprecated by Microsoft. The pioneering heroes of the old days who discovered how to actually
implement them have all adopted the new fashion of advising against using kernel hooks as a
programming practice. Often kernel hooks are unnecessary because there are documented ways which
allow a programmer to achieve his goal. However in a lot of system tools such as
monitoring and antivirus software, kernel hooks are the only available technique to get the
difficult job done and thus an unavoidable necessary evil. Important is that if your kernel system
services are hooked that you can find out which is the responsible software that makes use of these
techniques. Inspired by all the discussions going on about the Sony CD protection rootkit, we have
developed the RootKit Hook Analyzer.
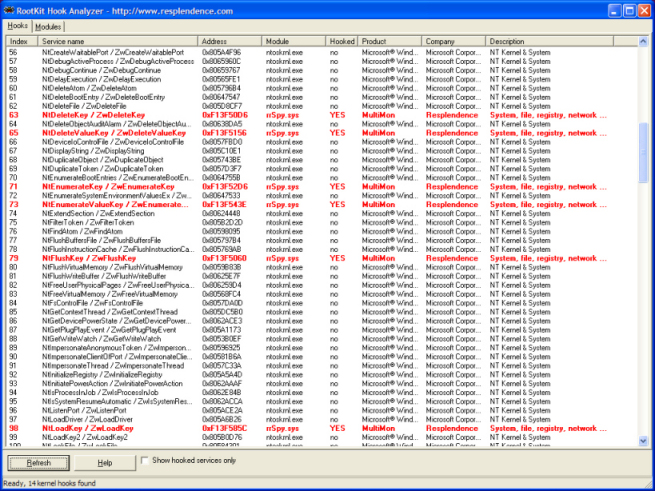
RootKit Hook Analyzer will tell you what kernel hooks are active on your system. It displays all
kernel system services along with their base addresses, responsible modules as well as product names
companies and module descriptions. If no hooks are active on your system it means that all system
services are handled by NTOSKRNL.EXE, the principal base component of most Windows operating
systems which is developed by Microsoft.
All you have to do to find out what kernel hooks are installed on your system is press the
Analyze button at the bottom of the screen. RootKit Hook Analyzer also allows you to view
installed system modules and drivers with their base addresses as well as file and product
information as well as the responsible companies.
Hook Quality Test
Free Download
RootKit Hook Analyzer is for free and runs on Windows Vista, XP, 2003 and 2000 (x86 editions only).
On a clean Windows installation, as soon as any application calls a system service from user mode, its
parameters will be checked for validity by the function which executes in kernel mode. This means
that if the application passes bogus parameters, it receives an error code and does not cause the
computer to crash. However if the system service is hooked and the hooked function does not do
proper parameter checking it can crash the system. One of the main causes for computer crashes
(blue screens and resets) these days is because legitimate programs (very often security
products) which do system call hooking do not properly validate their parameters.
With this test, you can check if the software you have installed does not suffer from this problem. If
your computer resets during this test it means the software you have installed is at fault. This
does not mean it is exposing rootkits or malware to your system but it means that it is
compromising your systems stability and probably causing your computer to reset or blue screen during
normal computer operation as well. If this test fails you should contact the author/vendor of the product
which is failing and notify him on the issue so he can hopefully set things straight and release an update.
Note: support for Windows x64 editions has been temporarily retracted and will be reintroduced
in a future release.
Click here to download Resplendence RootKit Hook Analyzer.
We will release a commercial version of the RootKit Hook Analyzer as part of a future
release of our advanced antivirus software Principal AntiVirus.
Copyright © 1997-2026 Resplendence Software Projects. All rights reserved. Privacy Policy.
Page generated on 2026-04-17 02:05:03 PM. Last updated on 2019-09-17 02:09:47 PM.
